Projects
My work seeks to facilitate a data-driven approach to enhance our understanding of the behavior of software systems as well as to build techniques to tackle their immediate, significant socio-technical problems.
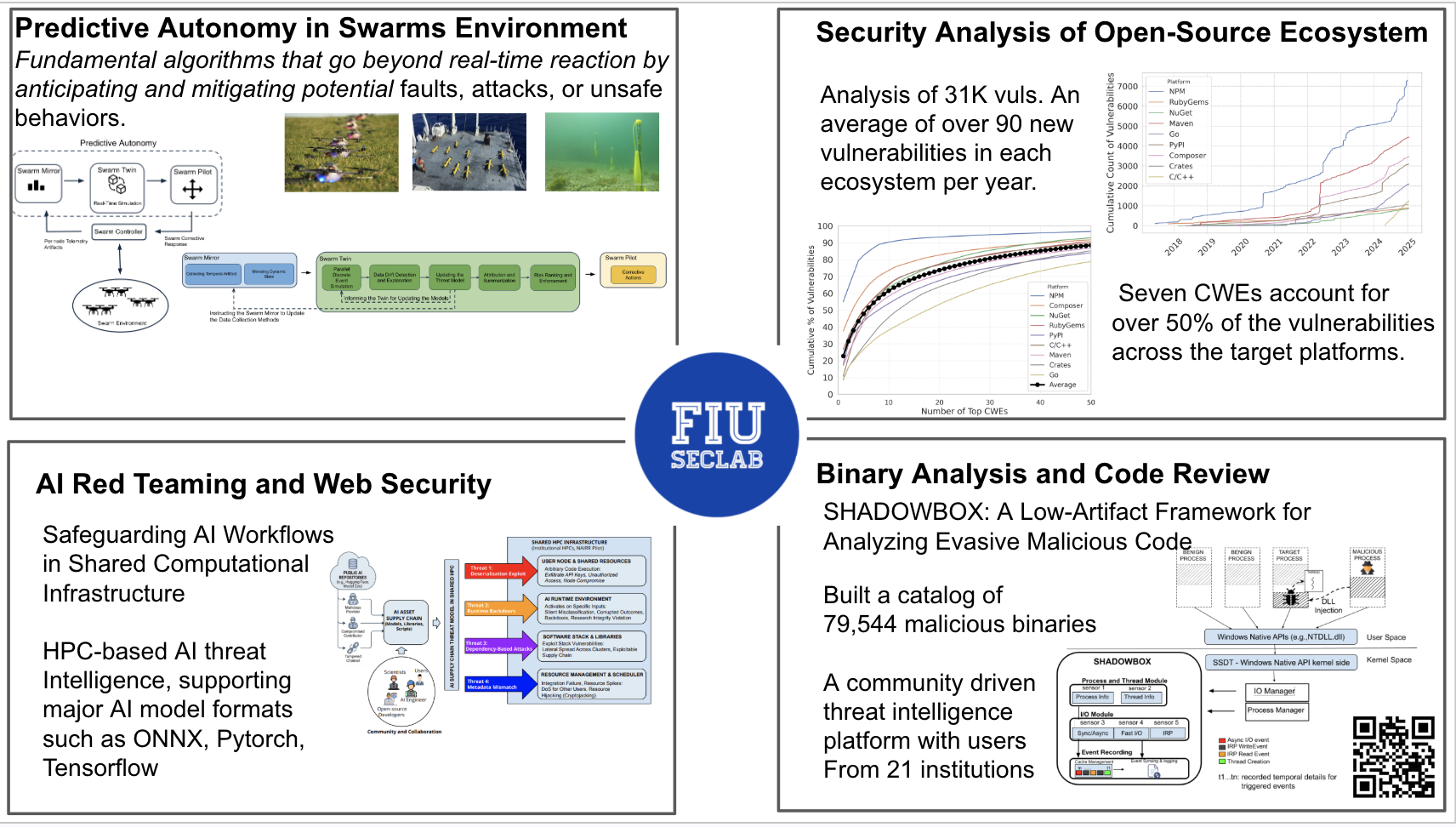
We study how adversaries exploit the dynamicity of the web — from in-browser cryptojacking and survey scams to malicious third-party inclusions and AI-driven agentic attacks on web services. Our tools detect and measure these threats at scale.
We build analysis platforms that generate semantically rich behavioral traces of malware, classify families automatically, and protect end-users at the OS level — without introducing perceptible performance overhead.
We measure how security mechanisms such as package signing and backup behavior work in practice, how vulnerabilities propagate through dependency graphs, and how attackers abuse trust in the open-source supply chain.
We empirically measure AI-driven threats — from adversarial attacks on security classifiers to large-scale CAPTCHA solving — and build uncertainty-aware, multi-modal systems that improve defender agility in real deployments.